Documentation Index
Fetch the complete documentation index at: https://docs.viewmargin.com/llms.txt
Use this file to discover all available pages before exploring further.
Authentication Method: Margin uses RSA key pair authentication to connect to Snowflake.
You’ll generate an RSA private key (
.p8 file) and configure the public key on your Snowflake user.If you encrypt your private key with a passphrase, you’ll need to enter it in Margin during setup.1. Snowflake Credential Setup
Margin needs a dedicated Snowflake user with:- scoped read access to the specific source schemas/tables you approve
- permission to create and manage schemas in a dedicated Margin database
How Margin Integrates
| Component | Description |
|---|---|
| Scoped read access to selected source tables | Lets Margin model from approved source tables while your team controls exactly what is exposed (including masking and explicit exclusions). |
| Dedicated Margin database access | Lets Margin create and manage its own schemas/tables for intermediate and final model outputs while keeping Margin artifacts isolated from your production databases and schemas. |
Margin does not write into your existing source schemas. Everything Margin produces lives in schemas created under your dedicated Margin database.
Create a Snowflake User
Below is a step-by-step guide to set up a Snowflake user with the necessary permissions:Generate RSA Key PairRun these commands in your terminal to generate your private key and public key:
If you set a passphrase, remember it. You will need to enter it in Margin.
| File | What to do with it |
|---|---|
rsa_key.p8 | Upload to Margin during setup (keep secure) |
rsa_key.pub | Copy contents into the ALTER USER statement below |
1. Create Margin Role/User
1. Create Margin Role/User
2. Create + Grant Dedicated Margin Database Access
2. Create + Grant Dedicated Margin Database Access
3. Grant USAGE on Source Data
3. Grant USAGE on Source Data
4. Grant SELECT on Specific Tables
4. Grant SELECT on Specific Tables
Copy and paste for each table you want Margin to read:
5. Mask Sensitive Columns (Optional)
5. Mask Sensitive Columns (Optional)
Configure the columns you want to mask in specific tables.
- Recommended: Use Option 1: built-in masking policies if you have Snowflake Enterprise.
- Otherwise, Option 2: secure views lets you expose a restricted projection.
6. Validate Dedicated Database Privileges
6. Validate Dedicated Database Privileges
Margin creates and manages its own schemas inside your dedicated Margin database.
This grants control only where explicitly allowed.
MARGIN_USER cannot create users/roles or access objects that are not granted to MARGIN_ROLE.If you need to connect to multiple databases, reach out to [email protected], we can enable this for you.
2. Snowflake Connection Configuration
A. Add a Snowflake Source in Margin
Go to your Integrations page in the Margin dashboard & click Add Source and select Snowflake.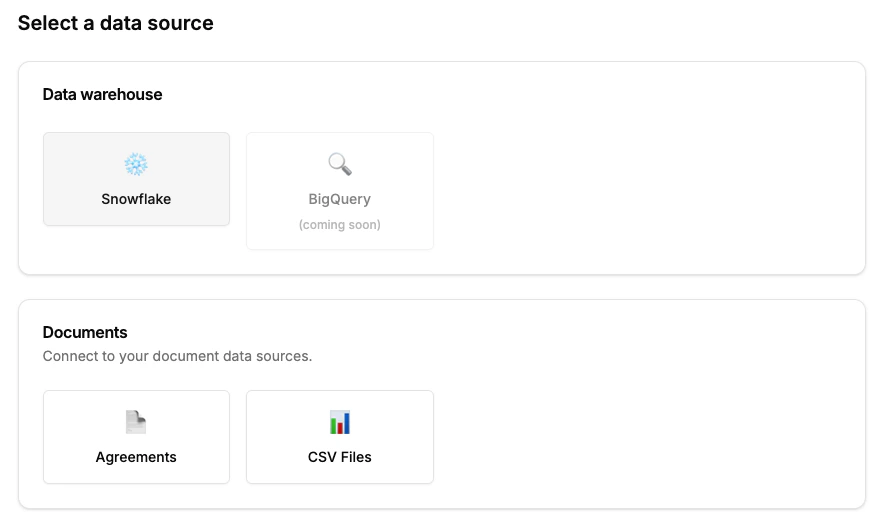
B.Enter Snowflake Credentials
Enter the following required fields into Margin:| Field | Description |
|---|---|
| Account Identifier | Account Name prefixed by its Organization (e.g. myorg-account123). Format may differ based on Snowflake account age. For details, visit Snowflake docs. |
| Warehouse | The warehouse name Margin should use to run queries. |
| Database | The default database for Margin queries. |
| Username | The Snowflake user you created (e.g., MARGIN_USER). |
| Private Key (.p8) | The RSA private key file generated during credential setup. |
| Private Key Passphrase | (Optional) Required if your private key is encrypted with a passphrase. |
| Role | The role you created (or an existing role with the necessary privileges). |
3. Testing the Connection
When you set up Snowflake, Margin verifies:- Basic connectivity check: Network connection & credential validation
- Verify user can create/manage schemas and objects in the dedicated Margin database:
- Schema lifecycle (CREATE, ALTER, DROP)
- Table lifecycle (CREATE, INSERT, SELECT, UPDATE, DELETE, RENAME, DROP)
- View lifecycle (CREATE, RENAME, DROP)
- Create/Drop STAGE
- Create/Drop FILE FORMAT
Troubleshooting
Common Issues
Common Issues
Authentication failures
- Ensure you’re using an RSA private key (
.p8file), not an SSH key - Verify the public key is set on your Snowflake user:
DESC USER MARGIN_USER - If you used a passphrase when generating the key, enter it in Margin
Permission errors during testing
- The wizard shows exactly which permissions are missing
- Ensure you completed Step 2 (dedicated Margin database permissions), Step 3 (schema USAGE), and Step 4 (table SELECT grants) in the setup script
Connection timeout
- Snowflake warehouses may be suspended—click “Test” again to retry
- Check that your account identifier format is correct
Next Steps
Once the connection is established, you can connect your finance sources to model over your event data.Sources: Finance Data
Connect your finance data sources